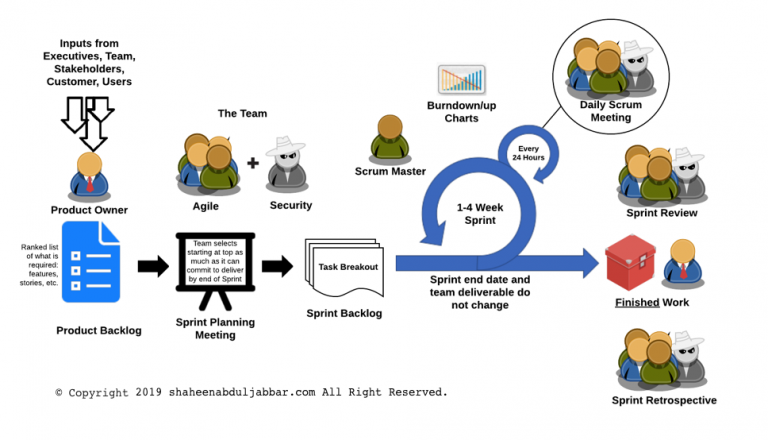
Many large organizations are moving towards the Agile software development lifecycle (SDLC) methodology. Agile methodology is a combination of iterative and incremental process models with a focus on process adaptability and customer satisfaction by rapid delivery of working software product. The general characteristics of any Agile methodology are: Prioritizing feedback. Agile teams rely heavily on the… Continue reading Security in Agile Methodology
Category: Security Architecture
Security Architecture and Models
Best of Breed or Best Suite of Products
Should organizations implement layered defenses from different vendors? Should we rely upon a single vendor for an organization’s overall security? According to a Gartner research paper, “Two firewall platforms are not better than one. We believe there is a higher risk associated with configuring and managing firewalls from multiple vendors than from a single vendor.… Continue reading Best of Breed or Best Suite of Products
Hardware or Host Based Firewalls
Do organizations need hardware firewalls when the network already has host-based software firewalls? Wouldn’t it add cost and complexity to networks? Wouldnt system protected by host-based software firewalls just as secure as having a hardware firewall if they are implemented appropriately? “Firewalls actually come in two distinct flavors: software applications that run in the background… Continue reading Hardware or Host Based Firewalls
Ralph Langner: Cracking Stuxnet, a 21st-century cyber weapon
When first discovered in 2010, the Stuxnet computer worm posed a baffling puzzle. Beyond its unusually high level of sophistication loomed a more troubling mystery: its purpose. Ralph Langner and team helped crack the code that revealed this digital warhead’s final target — and its covert origins. In a fascinating look inside cyber-forensics, he explains… Continue reading Ralph Langner: Cracking Stuxnet, a 21st-century cyber weapon
Intrusion Prevention System To Detect BotNet
The second half of the year 2010 saw stuxnet all over the news. Stuxnet, a cyber worm, is believed to be the world’s first publicly identified known cyber weapon. Such worms are designed to destroy the control system in a factory, refinery or even a nuclear power plant. Computers are infected with such worm through… Continue reading Intrusion Prevention System To Detect BotNet
Face Recognition Systems For Facility Access
Identity card issued by the employer is the typical mechanism to identify an employee. However, verifying each and every card presented by personnel requires a dedicated person or an automated system. Credentials, such as an identity card, are more effectively verified using an automated system. However, most of the verification systems are incapable of verifying… Continue reading Face Recognition Systems For Facility Access
Secure Mobile Device For Enterprise
With the introduction of cool mobile devices available for the corporate world, executives feel their existing blackberry out of fashion. For a while, blackberry devices ruled the corporate world for mobile communications. They are efficient and highly secure. Blackberry security is still considered the gold standard for enterprise mobile communications. However, with generation Y taking… Continue reading Secure Mobile Device For Enterprise
Risk Based Authentication
The technique that uses both contextual and historical user information along with data supplied during an internet transaction to assess the probability of whether a user interaction is authentic or not is called risk based authentication. Traditional username and password along with information such as who the user is, from where the user is logging… Continue reading Risk Based Authentication
Biometrics Authentication
Passwords and personal identification numbers (PIN) are information that we need to remember since the day we started interacting with digital systems. Do we know the count of passwords we need to remember? Do we know if we forgot a password already? Some of these passwords also known as passphrase are long to remember that… Continue reading Biometrics Authentication
ASP to SaaS
A discussion on business model transition from ASP to SaaS