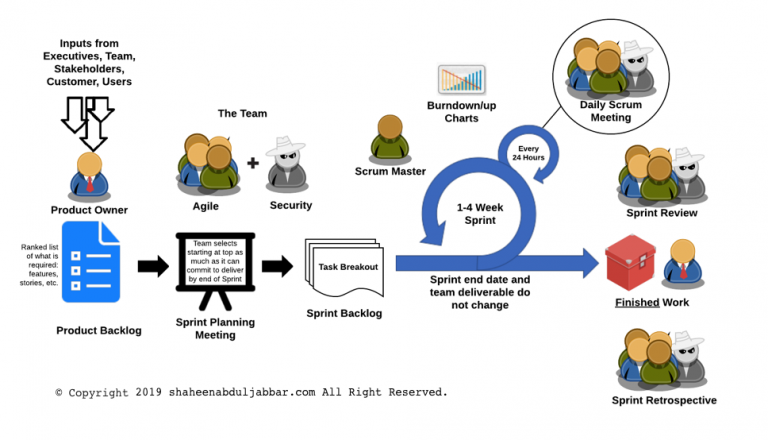
Many large organizations are moving towards the Agile software development lifecycle (SDLC) methodology. Agile methodology is a combination of iterative and incremental process models with a focus on process adaptability and customer satisfaction by rapid delivery of working software product. The general characteristics of any Agile methodology are: Prioritizing feedback. Agile teams rely heavily on the… Continue reading Security in Agile Methodology
Tag: Information Security
Best of Breed or Best Suite of Products
Should organizations implement layered defenses from different vendors? Should we rely upon a single vendor for an organization’s overall security? According to a Gartner research paper, “Two firewall platforms are not better than one. We believe there is a higher risk associated with configuring and managing firewalls from multiple vendors than from a single vendor.… Continue reading Best of Breed or Best Suite of Products
Hardware or Host Based Firewalls
Do organizations need hardware firewalls when the network already has host-based software firewalls? Wouldn’t it add cost and complexity to networks? Wouldnt system protected by host-based software firewalls just as secure as having a hardware firewall if they are implemented appropriately? “Firewalls actually come in two distinct flavors: software applications that run in the background… Continue reading Hardware or Host Based Firewalls
Cloud Computing and Data Security
We cannot attribute the beginning of cloud computing to a particular person or time. It evolved with the evolution of Internet and enterprise computing. We may be able to trace its roots all the way back when Dr. Larry Roberts developed the ARPANET in 1969. (Whitman & Mattord, 2016) While the evolution of ARPANET, to Ethernet… Continue reading Cloud Computing and Data Security
Roles of Management and Technology in InfoSec
Information security is both a management issue and a technology issue. The management of an institution could be the owner or custodian of the data that their information security program is trying to protect. They need to ensure that the systems they employ execute all the functions on the data as they are supposed to… Continue reading Roles of Management and Technology in InfoSec
Who doesn’t need to be concerned about InfoSec?
Would there be any person or group within an organization that does not need to be concerned with information security? The only person who need not worry about information security is the one who has no value bearing data. Unfortunately, in this day and age, every single person who is connected to modern world has… Continue reading Who doesn’t need to be concerned about InfoSec?
Secure Mobile Device For Enterprise
With the introduction of cool mobile devices available for the corporate world, executives feel their existing blackberry out of fashion. For a while, blackberry devices ruled the corporate world for mobile communications. They are efficient and highly secure. Blackberry security is still considered the gold standard for enterprise mobile communications. However, with generation Y taking… Continue reading Secure Mobile Device For Enterprise
Risk Based Authentication
The technique that uses both contextual and historical user information along with data supplied during an internet transaction to assess the probability of whether a user interaction is authentic or not is called risk based authentication. Traditional username and password along with information such as who the user is, from where the user is logging… Continue reading Risk Based Authentication
Disk Overwrite or Wipeout Best Practice
An online search shows majority of tools available for wiping out data on a disk points to a practice of 7 wipes. They believe that it is a US DoD requirement. Some of them support the Gutmann method of 35 wipes. However, I could not find any documentation on US government website that indicates seven… Continue reading Disk Overwrite or Wipeout Best Practice
Security Must Haves in a SaaS Provider
The past year was a learning curve on Cloud Computing, especially on SaaS providers. More and more ASPs are coming back rebranded as SaaS provider. As a security practitioner, it would be good to have a must have check list that we need to use to assess them. I prepared the following must have check… Continue reading Security Must Haves in a SaaS Provider