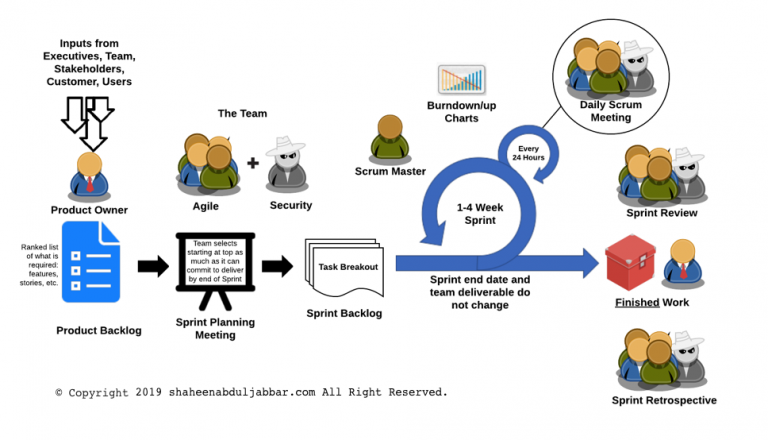
Many large organizations are moving towards the Agile software development lifecycle (SDLC) methodology. Agile methodology is a combination of iterative and incremental process models with a focus on process adaptability and customer satisfaction by rapid delivery of working software product. The general characteristics of any Agile methodology are: Prioritizing feedback. Agile teams rely heavily on the… Continue reading Security in Agile Methodology
Author: webadmin
Career in Cybersecurity
There was a time when you say you work in cybersecurity people would misunderstand you to be a security guard for some unheard company. Not anymore! Today cybersecurity is in the mainstream. If you are in the business of protecting internet-connected systems, including hardware, software, and data, from adversaries, then you are already a cybersecurity… Continue reading Career in Cybersecurity
MX Records on Amazon Lightsail
Are you considering moving your Name Server to Amazon Lightsail? You may end up looking for what that “subdomain” means for the MX records. As someone who volunteers for non-profits, I have the opportunity to try out Gmail from G-Suite. As of today (August 25, 2018), Google is yet to provide documentation for Amazon Lightsail… Continue reading MX Records on Amazon Lightsail
Best of Breed or Best Suite of Products
Should organizations implement layered defenses from different vendors? Should we rely upon a single vendor for an organization’s overall security? According to a Gartner research paper, “Two firewall platforms are not better than one. We believe there is a higher risk associated with configuring and managing firewalls from multiple vendors than from a single vendor.… Continue reading Best of Breed or Best Suite of Products
Hardware or Host Based Firewalls
Do organizations need hardware firewalls when the network already has host-based software firewalls? Wouldn’t it add cost and complexity to networks? Wouldnt system protected by host-based software firewalls just as secure as having a hardware firewall if they are implemented appropriately? “Firewalls actually come in two distinct flavors: software applications that run in the background… Continue reading Hardware or Host Based Firewalls
Acknowledging Non-Applicable Threats
Is it important to account for or acknowledge risks that may not apply to an organization or system? What if you identified a risk that you would typically consider for but would not use due because of the context. Say, for example, your organization is not in a floodplain however it is usual to consider… Continue reading Acknowledging Non-Applicable Threats